SCAM is an in-depth investigation of Southeast Asia’s online fraud and hacker industry and its human toll.


SCAM is an in-depth investigation of Southeast Asia’s online fraud and hacker industry and its human toll.

In the current age of digital technology, car owners are being forced to consider their vehicle’s susceptibility to ransomware attacks. These malicious cyber-attacks can expose your personal data to online hackers. However, there are certain measures that car owners can take to help prevent security breaches. Proactive car owners are utilizing services like Concentric to […]

According to a recent study by the Atlas VPN team, the United States, United Kingdom, and Saudi Arabia lead in commitment to cybersecurity. As technologies continue to evolve, governments around the world must face the reality of cyber threats and adapt their security practices. A study reports on countries’ scores on the Global Cybersecurity Index […]
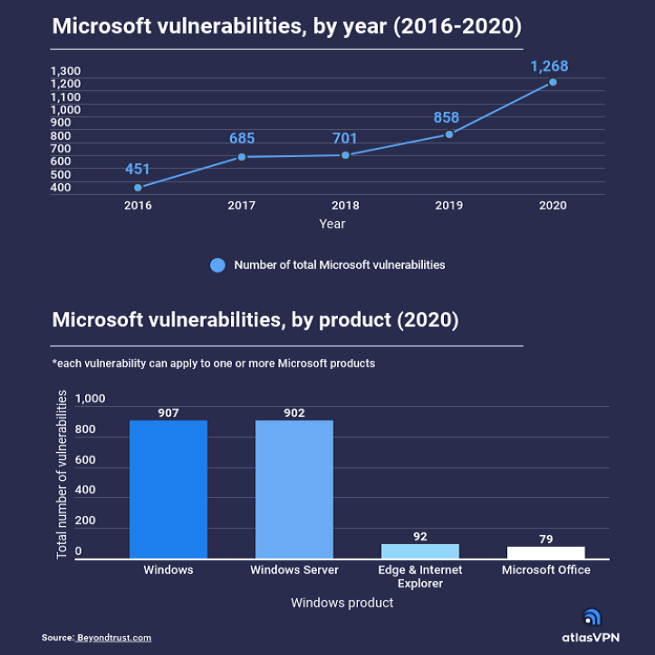
Microsoft products are used by billions of people worldwide. Historically, however, they are known to have many vulnerabilities that pose security risks to users of the software. According to data presented by the Atlas VPN team, the total number of vulnerabilities in Microsoft products reached 1,268 in 2020—an increase of 181% in five years. Windows […]

Amazon announced that it will be acquiring MGM Studios for $8.45 billion, in an effort to bolster the already growing Amazon studios and making it the second largest acquisition on Amazon’s part, following its $13.7 purchase of Whole Foods in 2017. According to cybersecurity expert Mark Stamford, CEO of OccamSec, a deal of this scale will require a […]
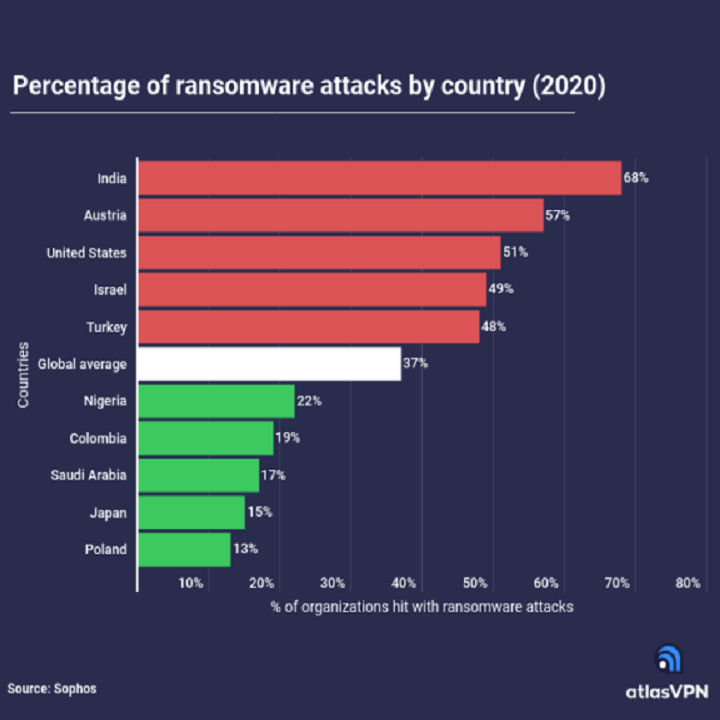
Ransomware attacks are one of the leading cyber threats that organizations have to face. According to the data presented by the Atlas VPN team, organizations in India, Austria, and the United States are among the most hit with ransomware attacks. To compare, more than 50% of companies in the mentioned countries experienced such attacks in […]

Biden’s Spending Plan for Education President Biden is planning to enact higher taxes on the wealthy to go towards free preschool, two years of free community college for young adults, and national paid leave. The 1.8 trillion spending and tax plan is aimed to expand education, while increasing the US’ social safety net, supporting women […]
Technology has become more and more important to how we live in recent years. This has seen high tech developments like contactless card payments, ecommerce and smartphones all become normalized in our lives. The foundation that most modern tech advances like this are built on is in the internet. It is this ability to head […]

A new study expects there to be an unprecedented rise in online romance scams this Valentine’s Day, with scammers praying on lonely and isolated people during the pandemic. Americans lost $201 million to romance scams in 2019, more than any other type of scam. Virginia had the eighth most victims in the nation. When the FTC releases […]

By Justin Lyons According to Italian press sources, Luxottica was the victim of a cyberattack Saturday. Luxottica owns eyewear brands like Oakley, Ray-Ban, Coach, Chanel and Versace as well as retail brands like LensCrafters, Sunglass Hut and Target Optical. It is the largest eyewear company in the world with more than 80,000 employees. SecurityOpenLab, an […]